Recently, Shellter has been added to the official repository of Kali Linux. This is a very important milestone in the course of development for this project. Since there are not many tools that can be used to assist penetration testers evading anti-virus (AV), we decided to write a few words about it.
What is Shellter?
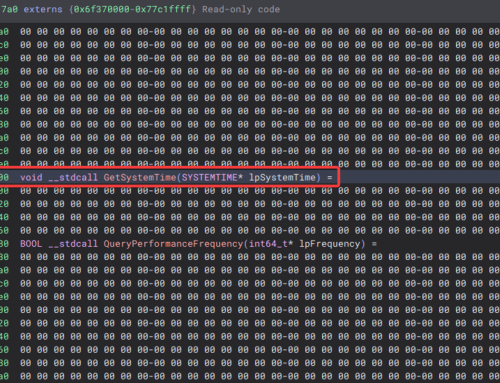
It is a truly dynamic shellcode injector. By ‘dynamic’ we mean that the start of the injected code does not occur in locations that are based on very strict rules, such as the entry point of an executable or at a statically predictable location. Shellter currently only supports 32-bit executables. This is a project that I have started and keep developing in my own time for the past two years.
How are the injection points selected?
The injection points are based on the execution flow of the executable. Shellter will actually trace the execution flow of an application in userland and it will log those instructions and locations that are in the range of the executable where the injection will take place.
Once the tracing has finished, Shellter will filter the execution flow based on the size of the code that is about to be injected and it will only consider the valid injection points based on various filtering parameters.
What other features does Shellter provide?
Even though avoiding the usage of static injection locations is a very important thing for AV bypassing, Shellter is not only limited to that, and it provides some additional advanced features.
More exotic features are currently being added in the upcoming version of Shellter that will be officially presented in public for the first time in BsidesLisbon 2015.
To contact Nettitude editor, please email media@nettitude.com.